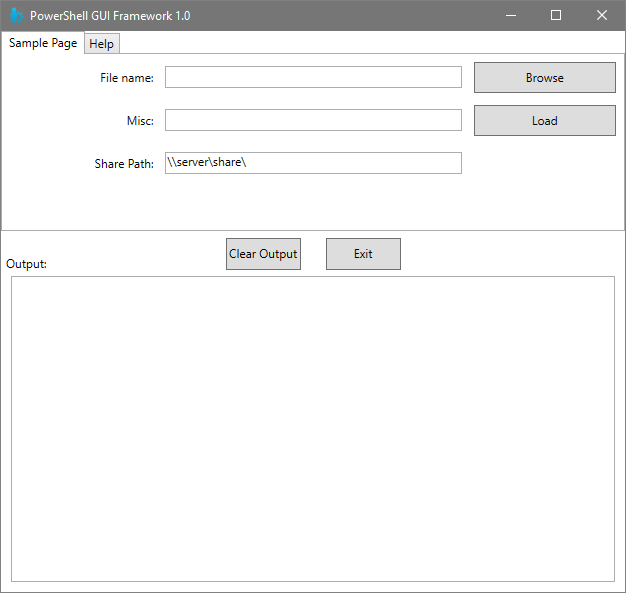
Syntax highlighting is one of the best features of a modern IDE or IDE-lite (such as VSCode). Things like IntelliSense, tab completion, matching token highlighting, go-to-definition, and more are all fantastic and make coding faster, easier, and more efficient (not to mention more accurate and consistent); however, a field of white text on a black background (or worse, black text on a white background) just makes everything look the same and hard to follow. Highlighting different tokens with different colors makes them stand out and makes it easier to tell what something is at a glance.
Read MoreSyntax Highlighting For Great Justice!